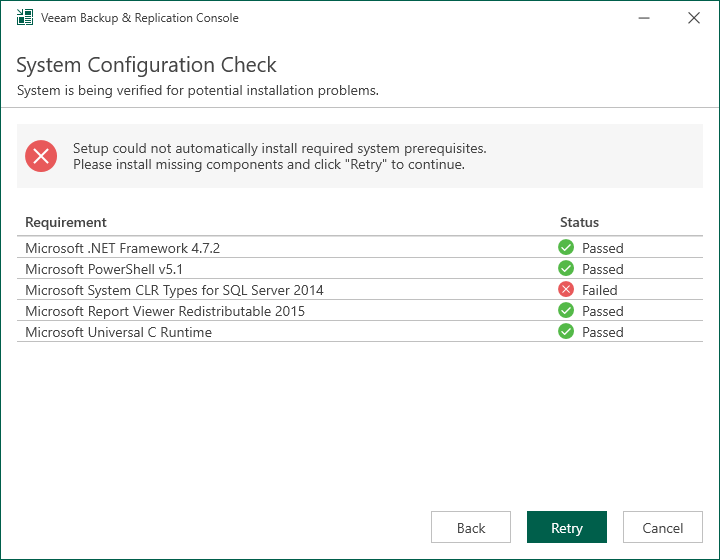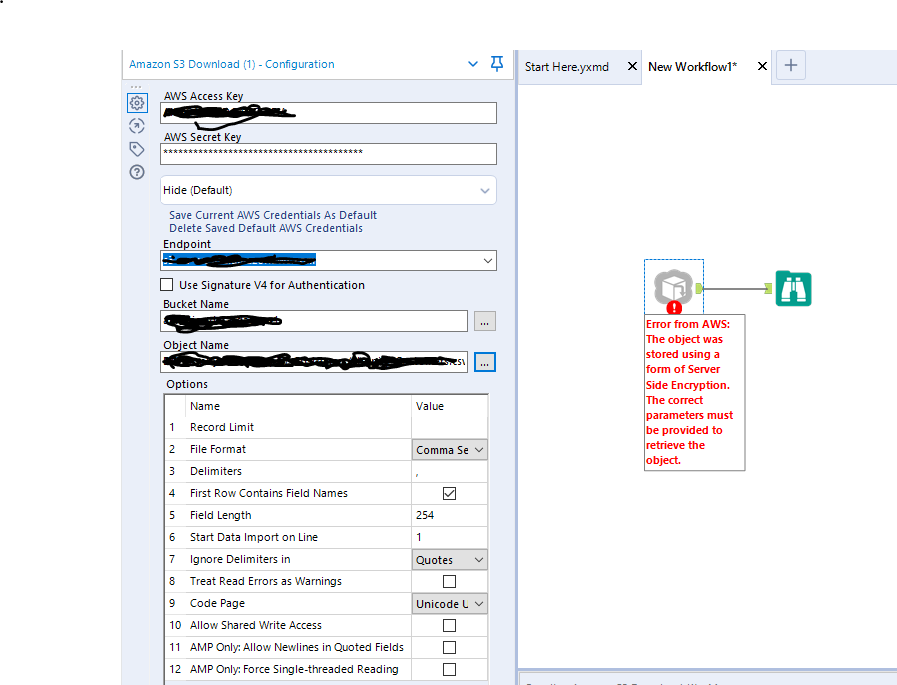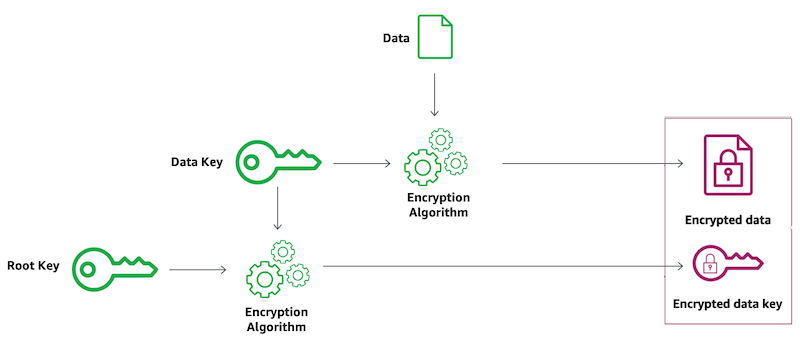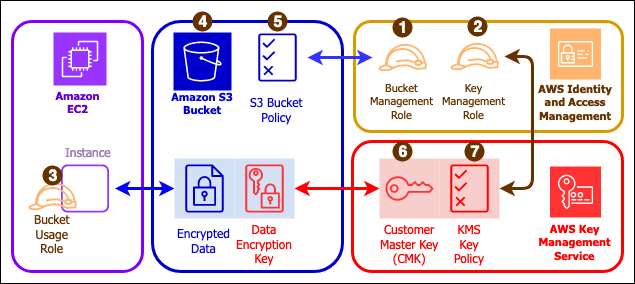
How to use KMS and IAM to enable independent security controls for encrypted data in S3 | AWS Security Blog
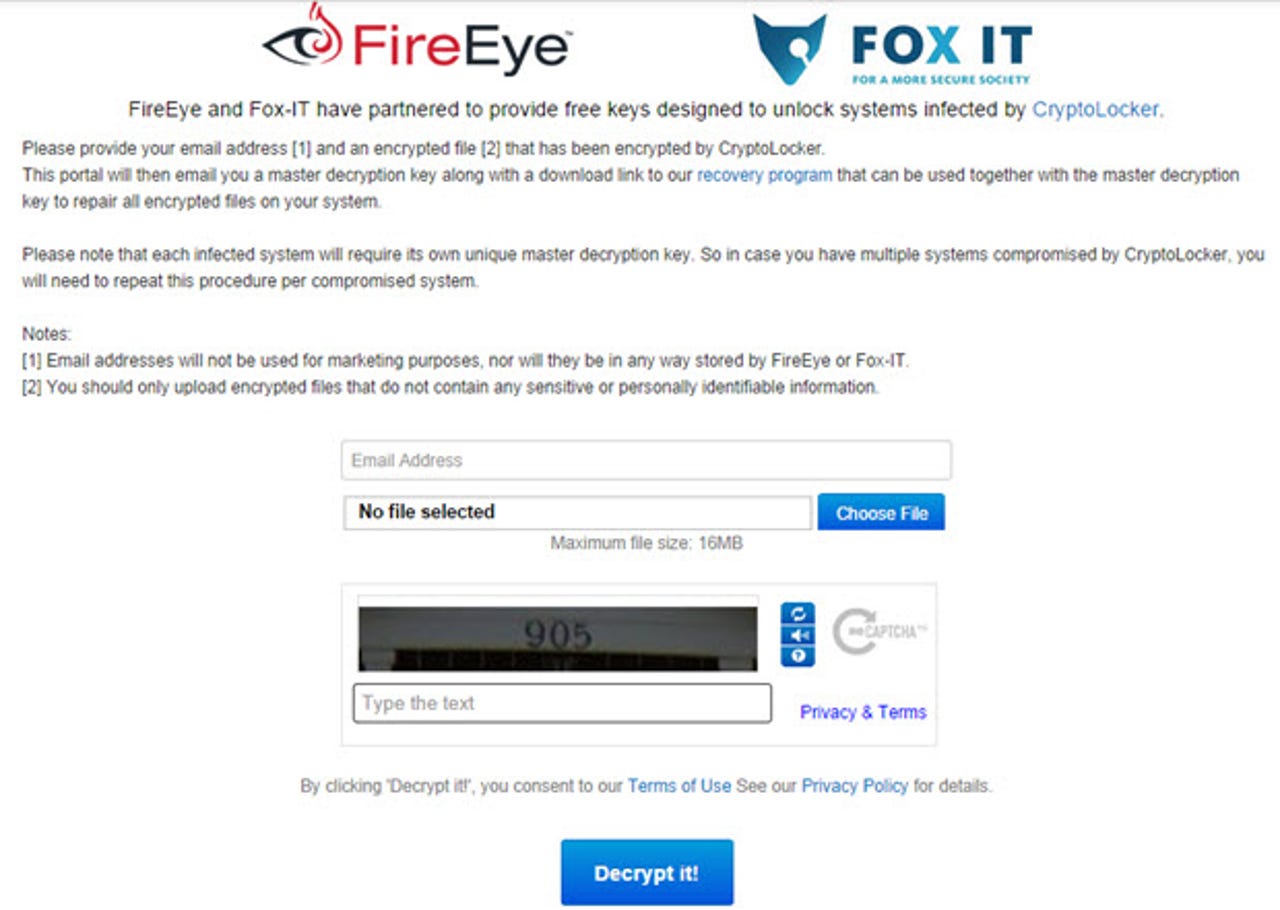
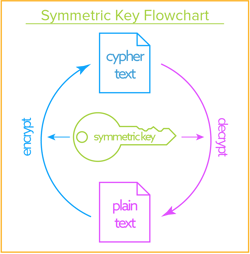
GitHub - tomrittervg/decrypt-windows-ec2-passwd: Amazon EC2 Windows Instances require you to paste in your SSH private key to decrypt the password to the instance. Although they do the decryption locally, in Javascript, I'd
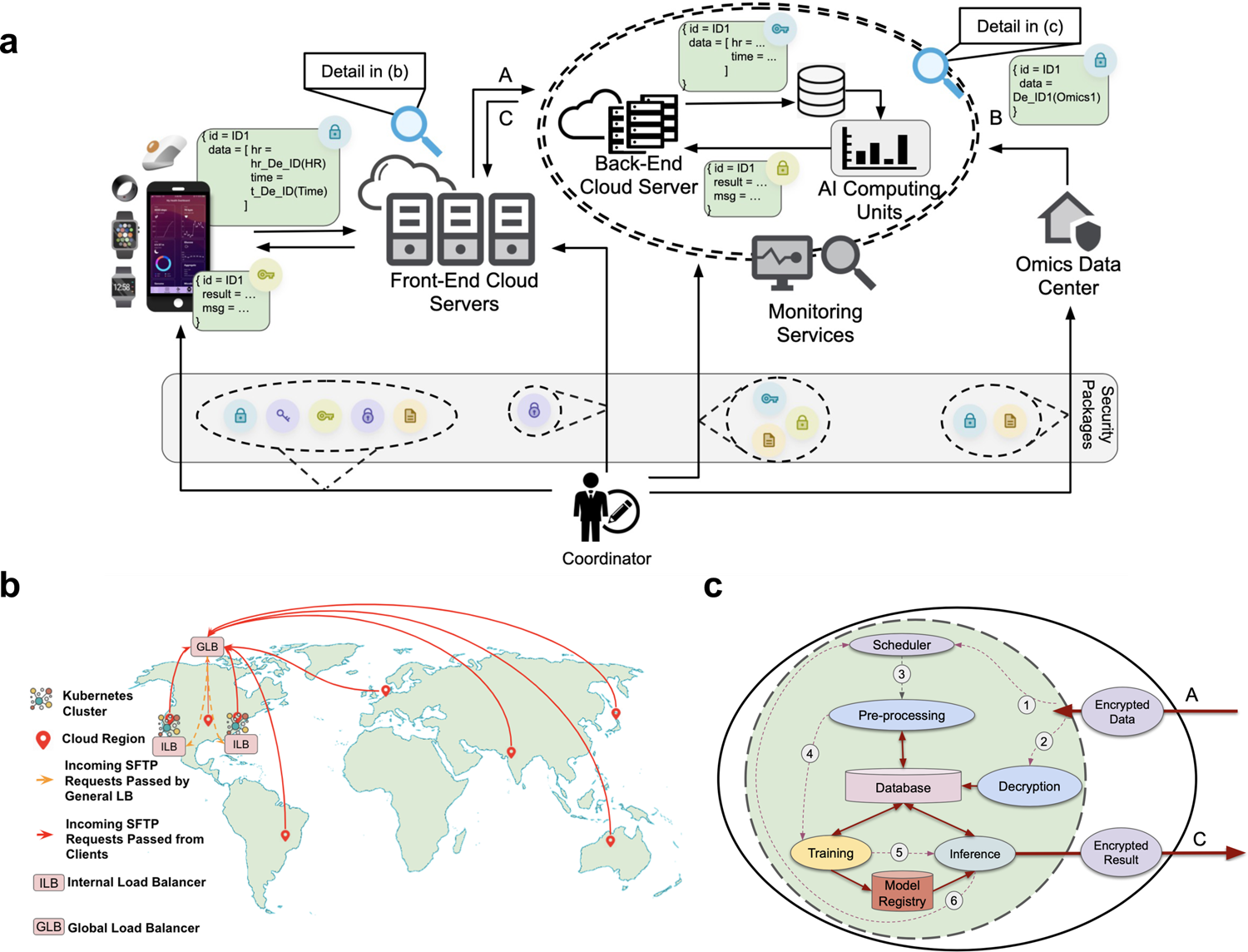
A scalable, secure, and interoperable platform for deep data-driven health management | Nature Communications
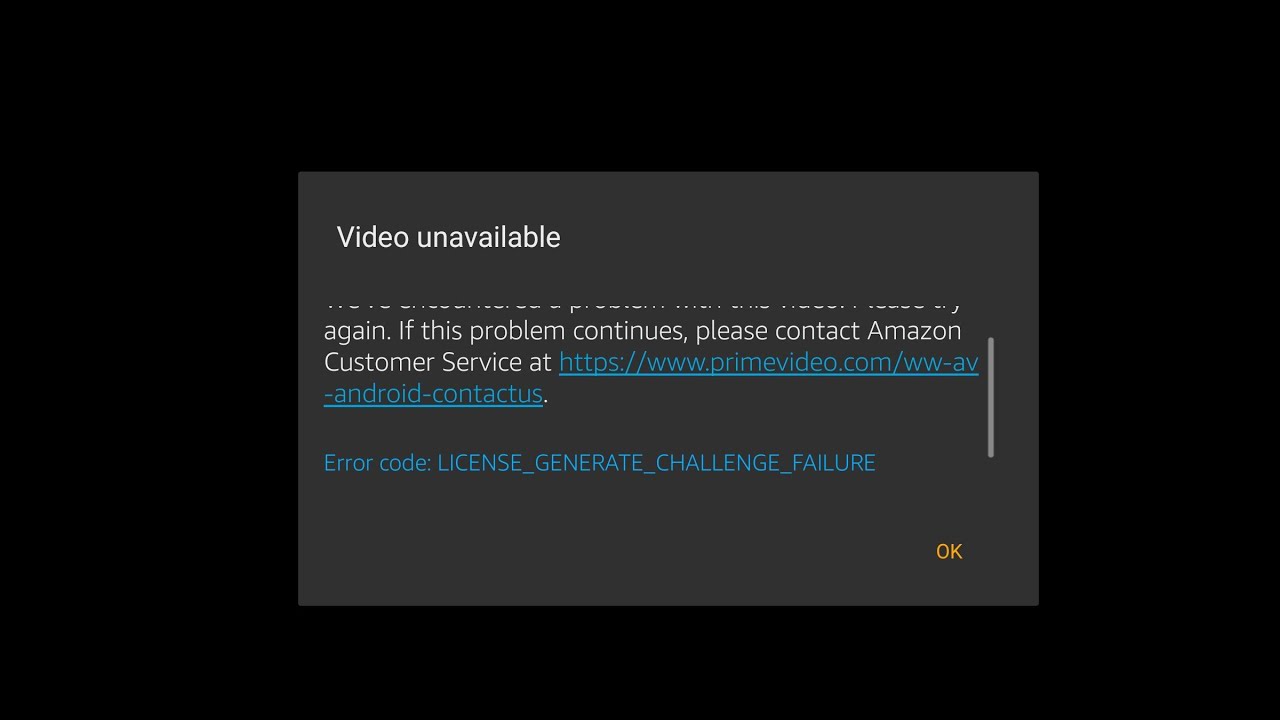
Whose Encryption Key is this?. How a subtle configuration can result… | by David Levitsky | Simply CloudSec | Medium