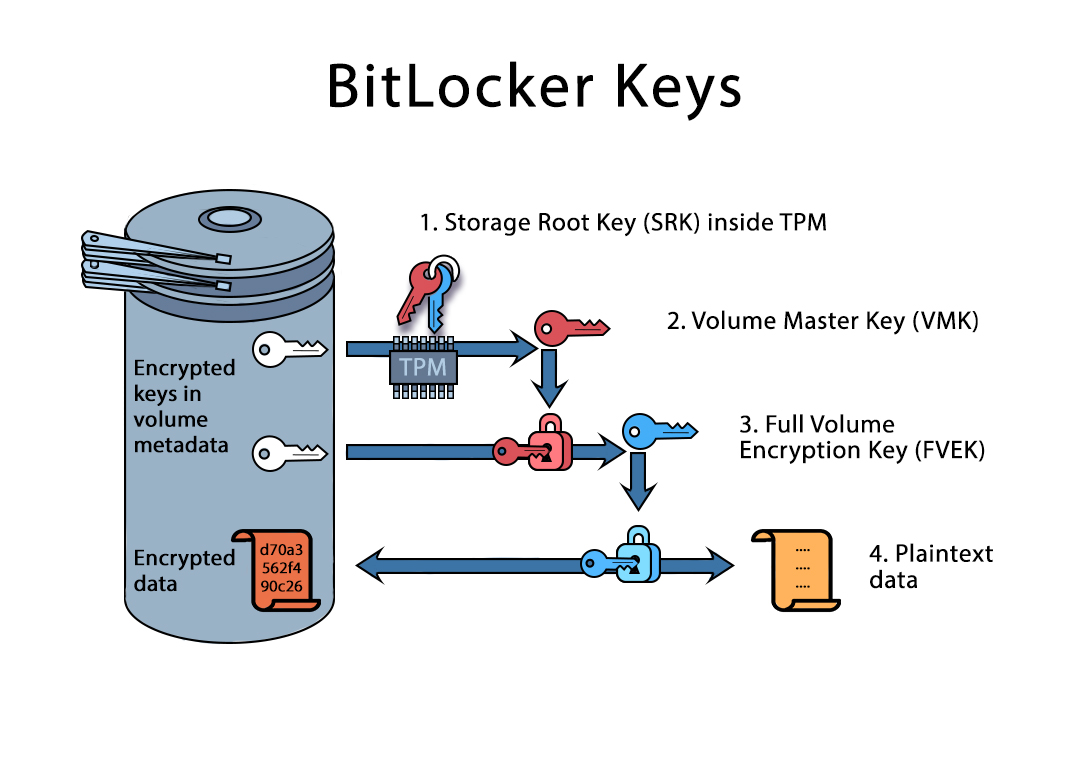
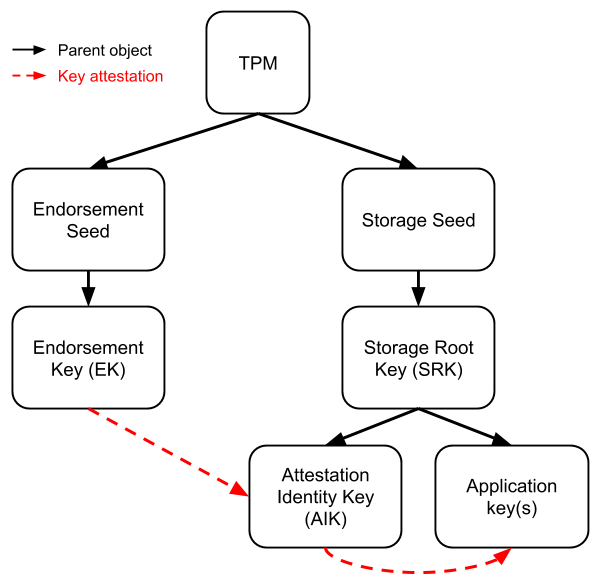
TKM Key Hierarchy Having in mind that TPM protected keys are bound to a... | Download Scientific Diagram

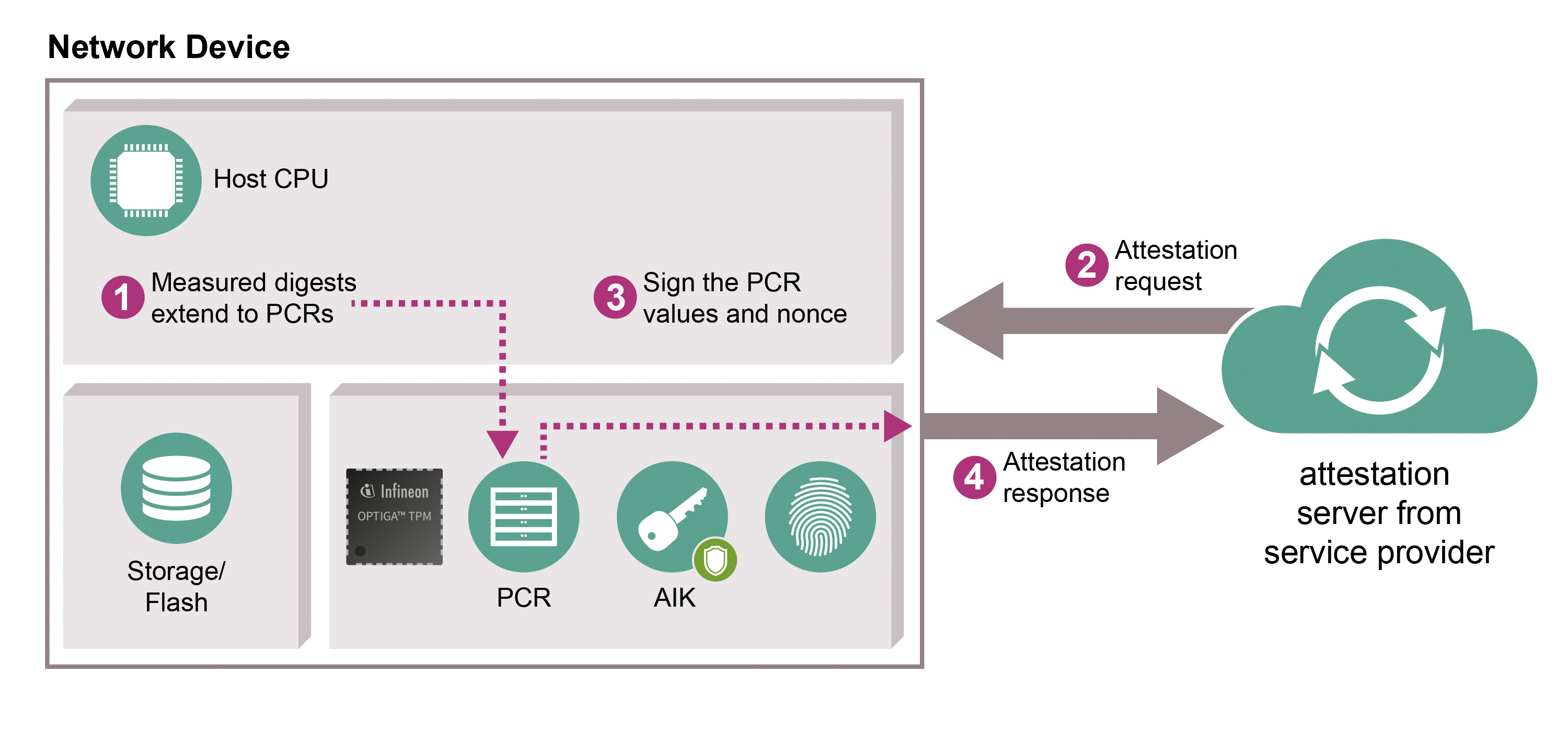
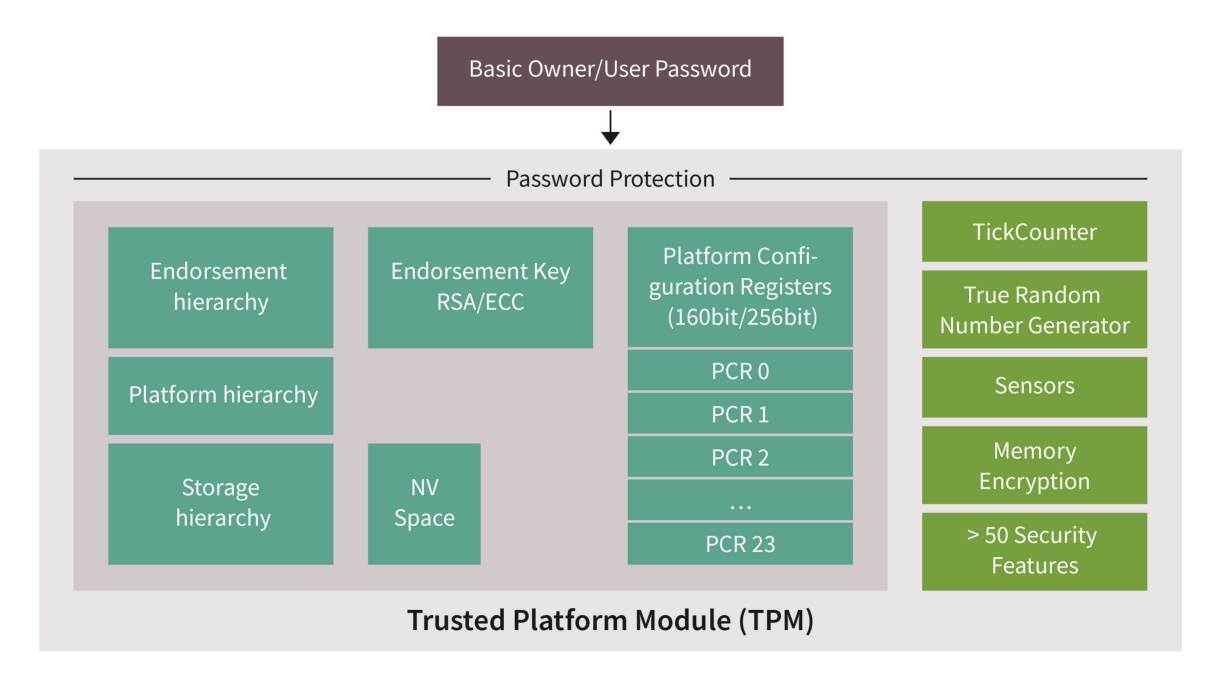
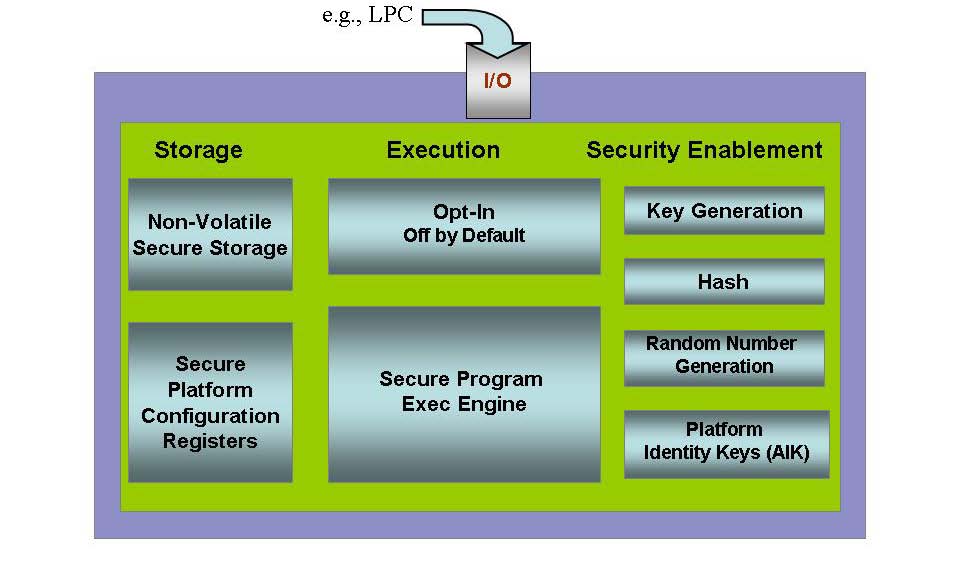
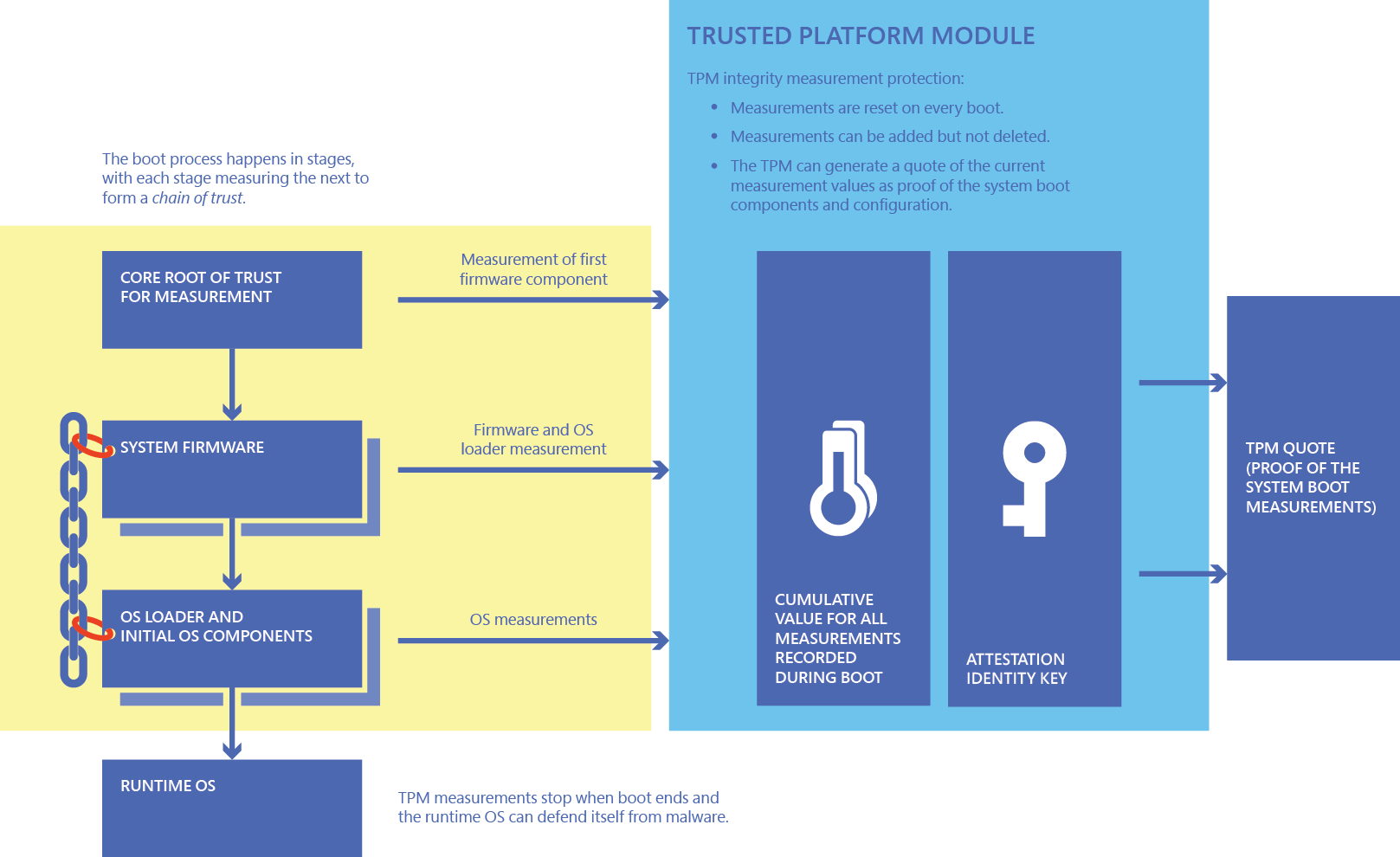
Basic Functionalities of a Trusted Platform | Trusted Computing Platforms, the Next Security Solution | InformIT

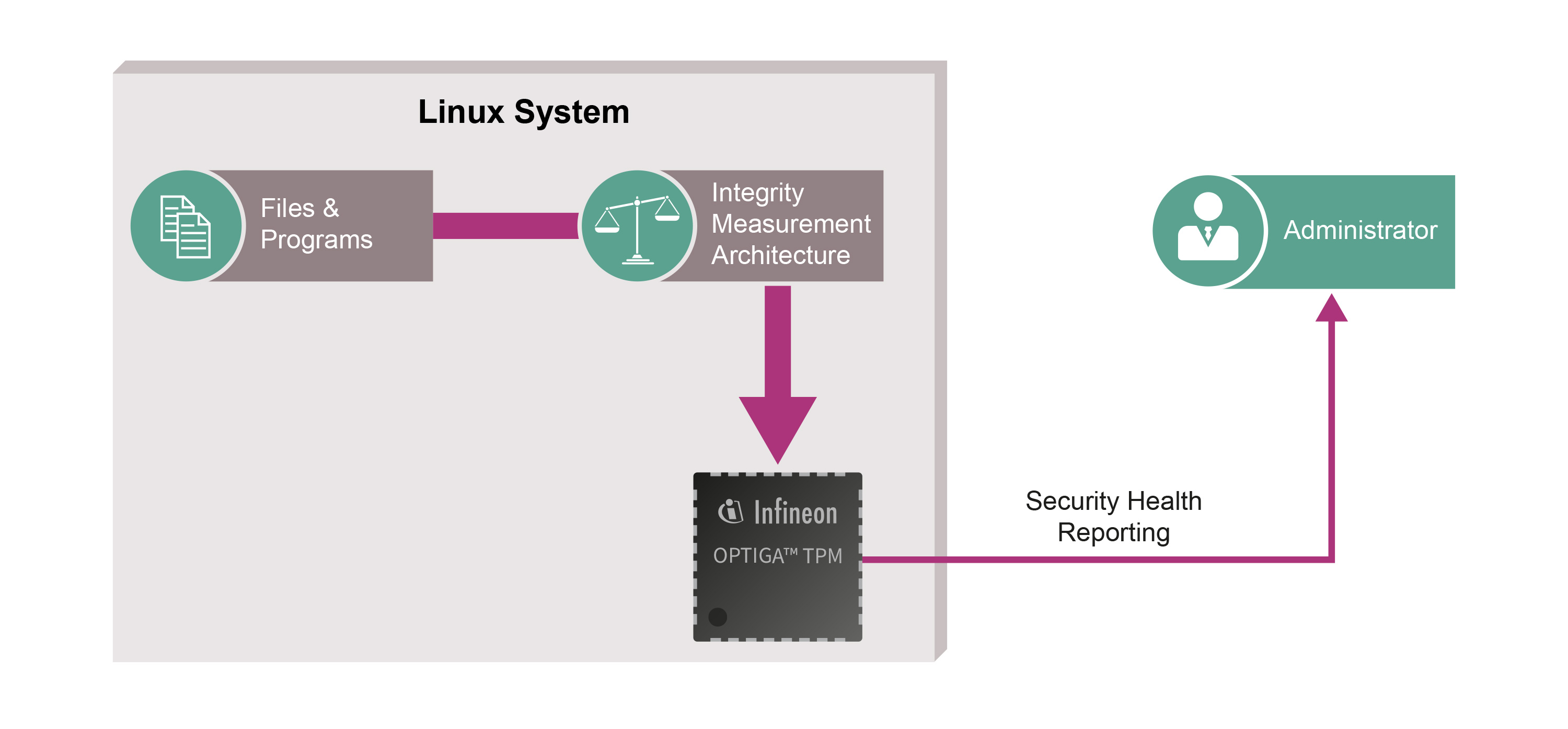
D3.9: Study on the Impact of Trusted Computing on Identity and Identity Management: Future of IDentity in the Information Society
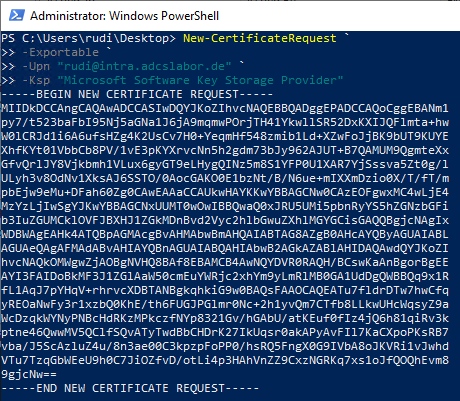
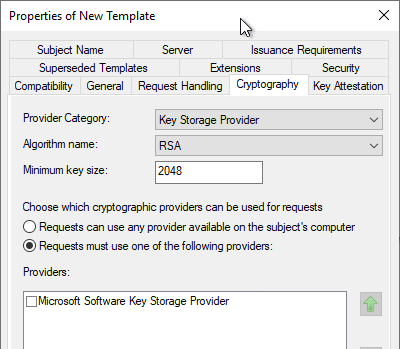
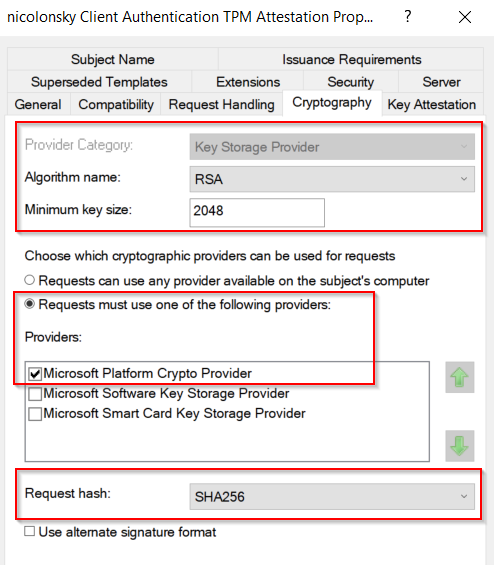
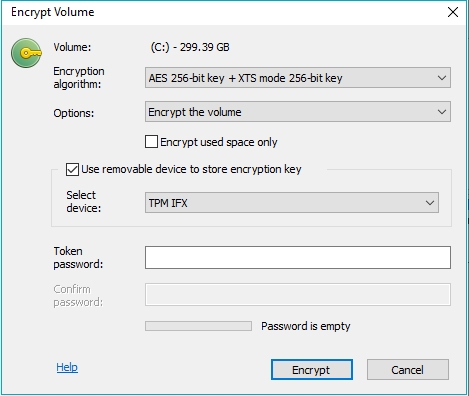
Beantragen eines durch ein Trusted Platform Modul (TPM) geschütztes Zertifikat – ohne ein TPM zu besitzen – Uwe Gradenegger

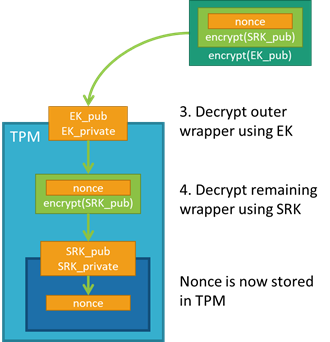
Data firewall trusted platform module (TPM) key tree. SRK: storage root... | Download Scientific Diagram